Cyber blind spots
We surveyed companies large and small to understand the cybersecurity bad habits that can impact businesses in the UK.
In a digitised economy, how prepared are small businesses to face cyber threats?
With the shift towards hybrid-working and changing consumer expectations, a digital offering is a necessity for all modern businesses. This exposes businesses to new risks.
Small businesses are particularly vulnerable. According to the latest government data, 38% of small businesses suffered a cyber breach or attack in the last year, with the average cost of an attack over £8k.
Superscript's research shows that a lack of engagement by employees is leading to bad habits which are putting SMEs more at risk. Nearly half (45%) of employees say they are not concerned about their business’ cybersecurity, with over a third of workers unaware of what cybersecurity measures are in place.
Scroll down for our key insights on employee attitudes towards cybersecurity at work, where they’re most complacent, and what small businesses can do to address the bad habits that result.
Password security
The belief that businesses should have invested in robust cybersecurity solutions has led to employee dismissiveness around several security measures. Password security is one particular area where employee complacency is creeping in:
- 15% of employees use a single password across all their professional accounts; compared to only 4% with their personal accounts. Indicating they take their personal security more seriously.
- 31% of workers have shared private passwords for professional accounts, opening businesses up to additional risk.
- A third indicated that they have previously changed a secure password to one that did not meet best practise (without special characters or numbers). When switching to a less secure password, 62% surveyed stated that their new password is easier to remember.
Password influences
How do people pick their passwords? Most common influences are:
- People’s names (e.g. children names, fictional characters, friends, celebs)
- Randomly generated
- Place names (i.e. towns, cities)
- Numbers
- Animals (pets)
- Things/objects
- Key calendar dates
- Bands/musicians
- Sports teams
- Food
The names of people we know are revealed as the most common influence for passwords. When deciding on your passwords, it is best to avoid using names of family members or your favourite Harry Potter character as it might put you at greater risk, with the chart to the right showing it’s a pattern of behaviour that can be easily exploited.

Logging in – additional authentication methods
Despite the development and implementation of new systems, employees are still hesitant to trust new authentication technologies over traditional password systems.
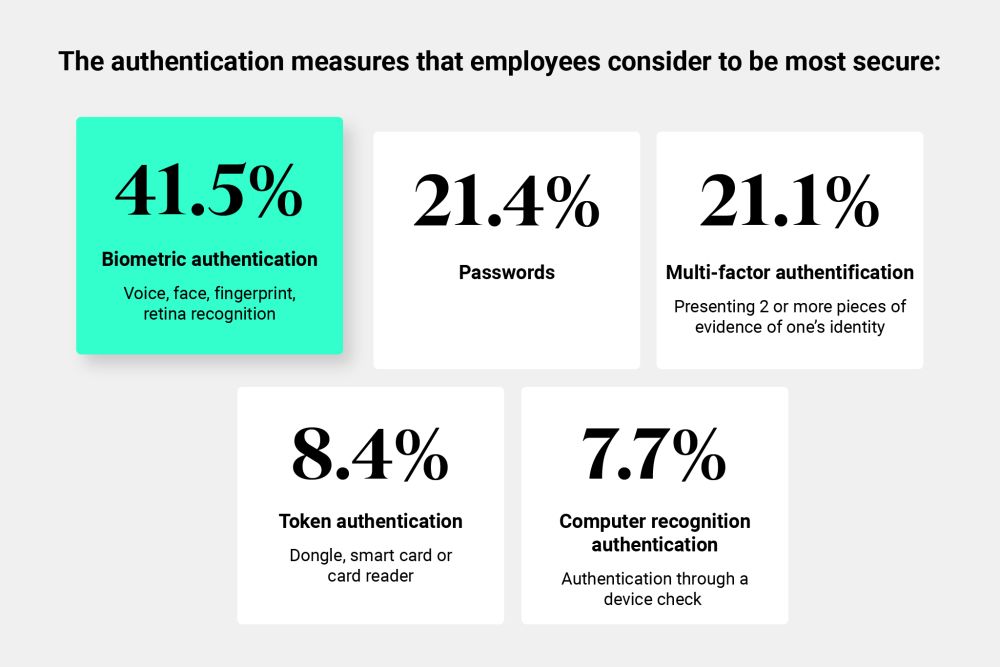
The authentication measures that employees consider to be most secure are the following:
- Biometric authentication i.e. voice, face, fingerprint, retina recognition (41.5%)
- Passwords (21.4%)
- Multi-factor authentication i.e. presenting 2 or more pieces of evidence of one’s (21.1%)
- Token authentication e.g. dongle, smart card or card reader (8.4%)
- Computer recognition authentication e.g. authentication through a device check (7.7%)
Multi-factor authentication is an issue for employees when it comes to ease of use. Employees are pretty split on how comfortable providing additional details such as mobile phone numbers to third parties (50% said they are comfortable, 50% not), while 40% regard multi-factor authentication as an overly inconvenient process. The move towards more seamless logging-in factors is part of the reason bad passwords habits are creeping in.
Employee awareness
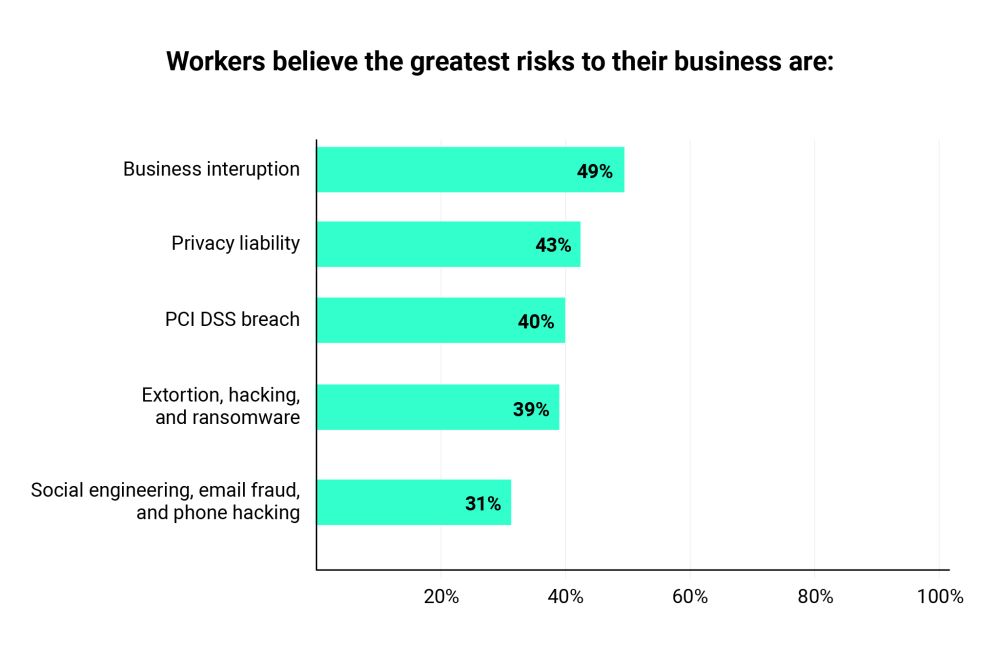
While there has been a lot in the news around ransomware and hacking recently, workers believe the greatest risks to their business are:
Business interruption – your business suffers a loss of income because of a cybersecurity breach affecting your or your suppliers computer systems
Privacy liability – your business is liable for damages incurred because of a data breach, a security or data breach (or your organisation’s failure to disclose such a breach) and failure to comply with certain parts of your privacy policy
Payment card industry data security standard (PCI DSS) breach – despite your business being PCI DSS compliant to reduce the risk of data breaches involving customers’ card details, private card data does leave your system
Extortion, hacking and ransomware – if your business is held at ransom by a hacker, or have to pay compensation to your customers because of a data breach
Social engineering, email fraud and phone hacking – your business experiences financial losses caused by funds transfer fraud (social engineering), phone hacking, botnet attack and cryptojacking
CyberSmart’s top 5 security tips
What measures can businesses take to shore up their cybersecurity? Our partner CyberSmart gave us some pointers:
1. Update your systems and software regularly
While you and your business may not have the resources nor manpower to fix vulnerabilities yourself, the big players do. They are constantly identifying and remediating, or ‘patching’, those flaws through software updates.
Therefore, it is important that operating systems, apps, web browsers and other software are updated every few days. You could even set company devices to auto-update.
2. Install basic cybersecurity protections
Another step you can take is to install basic protections like anti-virus, anti-malware software, and a firewall. The former will help scan your devices and files for malicious software, and remove them once identified. The latter will monitor incoming and outgoing network traffic, patrolling it for any suspicious activity.
3. Use multi-factor authentication and practice good password hygiene
Make sure all employees are meeting password best practices, using long, complex and unique passwords across their accounts. Using a password manager is a useful tool to help with this. Equally important, is enabling multi-factor authentication (MFA) wherever possible.
4. Back up your data
To ensure important data is not lost during a cyber-attack, you need to regularly back it up. Even better, you should back your data up on an offline drive. This ensures it can be recovered quickly and reduces the leverage cybercriminals have to blackmail you.
5. Implement security awareness training
To make good cybersecurity practices a habit and part of the company culture, organisations must build a supportive environment where it is okay to ask questions as many cybersecurity attacks succeed because someone was afraid of looking silly. It is also crucial that continuous cybersecurity training is carried out to address the specific knowledge gaps in your organisation.
Many cybercriminals will frequently leverage people’s heightened emotions (e.g a phishing email that uses fear to push someone to click a malicious link) or risky behaviours (e.g employees who use the same password across accounts), to hack into your systems. As such, we need to make a conscious effort to educate employees on their role in defending the company as well as empowering them with the knowledge and tools to combat those threats.

Authorised by the FCA
The FCA supervises UK financial services firms to protect consumers. We are directly authorised and regulated by the FCA and our Firm Reference Number is 656459. These details can be confirmed on the Financial Services Register at www.fca.org.uk or by calling the FCA on 0845 606 1234.
A-rated financial strength
Our insurance products are underwritten by Standard & Poor’s A-rated financial strength or higher. This means the underwriter has been independently assessed by the world’s leading credit rating provider and found to have a strong capacity to meet financial commitments (pay claims).
Protected by the FSCS
If you are a business with an annual turnover under £1m, charity with an annual income under £1m, or trust with net assets under £1m, then you will be entitled to compensation from the FSCS in the unlikely event we cannot meet our obligations. Full details and further information on the scheme are available at www.fscs.org.uk.



